Best News To Selecting Credit Card Apps
Wiki Article
How Can I Find Out Whether My Credit Card Was Reported As Stolen In The Us?
Follow these steps: 1. Contact the credit card company that issued your card.
Call the number listed on the backside of the credit card.
You may ask the representative to verify the status of your card.
You will be asked to verify your identity through providing your personal information and credit card details.
Check Your Online Account-
Login to your account online for credit cards or banking.
You can look for notifications, alerts and other messages about the status of your card.
Examine your most recent transactions for suspicious or illegal transactions.
Monitor Your Credit Report
Obtain a free copy of your credit report from each of the three major credit bureaus (Equifax, Experian, TransUnion) through AnnualCreditReport.com.
Examine the report for any unusual credit accounts or inquiries that might indicate fraud.
Fraud Alerts and Security Freezes--
You may want to consider putting a fraud alert, or security freeze, on your credit report in the event that you suspect theft or fraud involving personal information may have occurred.
A fraud alerts lenders to check your information prior to they extend any credit. The security freeze however is a restriction on access to your report.
Be Alert and Report Any suspicious activities
Check your credit card statements regularly and immediately notify any suspicious or unauthorised transaction.
Inform anyone who suspects identity theft or fraud to the Federal Trade Commission. Also make a complaint to your local police agency.
Contacting the company that issues your credit card by reviewing the activity of your account online, keeping an eye on your credit report and staying vigilant for any signs of unauthorized activity It is possible to take proactive steps to safeguard yourself from credit card fraud and resolve any issues with a reported stolen credit card.

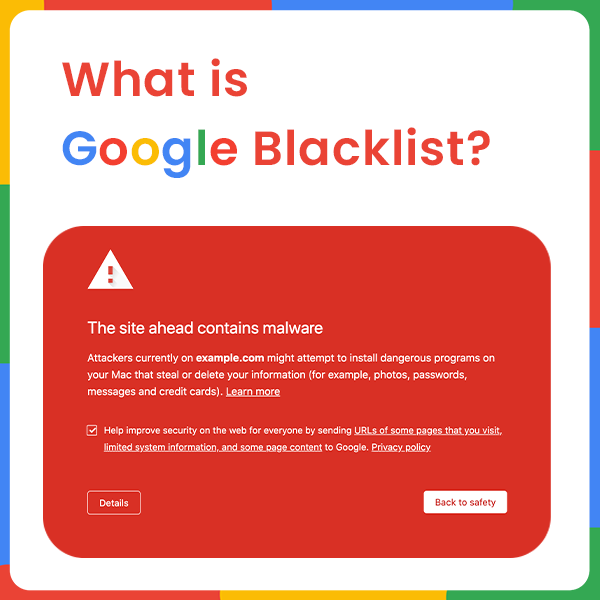
What Should I Do In The Event That My Credit Card Is On A Blacklist For Credit Cards?
If you think your card might be on a blacklist, or there is fraudulent activity linked to your card, immediately notify the card issuer.
You can dial the number for customer service on the back of your card or visit the website of the issuer to see if they have an anonymous hotline for reporting fraud.
Let the issuer know of any concerns you may have, such as an suspicion that fraud is taking place or that your credit card has been compromised.
Report Suspicious Activity-
Report any unusual or unauthorized transactions on your account.
Provide specific details about the transaction in question. Please include dates, figures and, if you can, merchant names.
Request Card Blocking, or Replacement-
To avoid any further unauthorized transactions To prevent future unauthorized transactions, request that your credit card provider temporarily block your card temporarily.
Inquire about the process for changing the card to a new one that will allow you access to credit.
Review Your account and Dispute Charges
Check your latest statements and transactions to identify any suspicious activity you may have missed earlier.
If you discover unauthorized transactions, dispute the transactions with your credit card issuer to ensure that they are looked into and resolved.
Keep Track of and Monitor Your Credit
Make sure to contact your credit card company to find out if the issuer has taken the correct steps to resolve any issues you might face.
Check your credit card balance regularly for unusual activity or sudden changes.
Think about putting up a Fraud Alarm or Security Freeze
You might want to place a fraud warning or security freeze in your credit report, based on the severity of the problem is. This can prevent fraudulent activity or identity theft.
Report to Authorities, if Needed
Notifying the Federal Trade Commission or filing an investigation with local law enforcement is highly recommended in the event of suspicion of substantial fraud.
You must take action immediately to reduce the risk of loss and to prevent the occurrence of unauthorized transactions. By reporting any suspicious activity immediately and cooperating with your credit card company, you can reduce the impact of potential fraud or abuse of your credit card.
Cybersecurity Experts Can Track And Identify Cyber-Threats, Including Ones That Involve Compromised Credit Card Data.
Security experts in cyber security monitor and spot security threats like stolen credit card numbers by using various techniques and tools. The most popular strategies and methods are: Threat Intelligence Gathering
Collecting information through different sources like forums, dark-web monitoring, threat intelligence feeds, and security advisories to stay current on the latest threats and weaknesses.
Network Monitoring and Intrusion Detection
Monitor the network's traffic with specialized tools or software. Find out if there are any suspicious behaviors that could indicate unauthorized entry or data breach.
Assessment of vulnerability and Penetration TestingVulnerability Assessments and Penetration Testing
Regular assessments are conducted to find vulnerabilities in systems, applications or networks. Testing penetration tests mimic attacks in order to find vulnerabilities and evaluate the security capabilities of an organization.
Security Information and Event Management, (SIEM),
Implementing SIEM Solutions that aggregate and analyse log data from various sources (such servers, firewalls and applications), to detect and respond in real time to security-related incidents.
Behavioral Analysis
Using behavioral analysis to detect odd patterns or variations from normal user behavior in systems or networks, which could signal a risk of compromise.
Threat HuntingThreat Hunting
By analyzing logs and data from systems, you are able to detect threats within your organization's network.
Endpoint Security Solutions-
Protection of systems and devices from malicious activity by deploying endpoint security products, such as antivirus, antimalware, and endpoint detector and response (EDR) tools.
Encryption, Data Protection and Privacy-
Implementing encryption techniques to safeguard sensitive data, such as credit cards when it is transferred and stored it will lower the likelihood that data breaches occur.
Incident Response and Forensics
Implementing an incident response plan can allow you to swiftly respond to any incidents. Conducting forensic analysis in order to comprehend the impact, scope and root causes of security breaches.
Cybersecurity experts combine these strategies and a deep understanding with guidelines and best practices for compliance to detect, reduce and swiftly respond to cyber threats. To be able to defend yourself against cyber threats it's essential to stay on top of continuous monitoring, intelligence and an active approach. Read the recommended savastan0 review for more info.